
The DeFi industry has been in panic mode the entire week. On April 18, 2026, Kelp DAO suffered a ~$290 million exploit involving its rsETH token. The attacker triggered a forged cross-chain message through LayerZero, causing the protocol to release 116,500 rsETH from its bridge escrow on Ethereum—without any corresponding deposit or burn on the source chain.
Technically, the exploit did not rely on a smart contract vulnerability. Instead, it abused the verification layer. Kelp DAO’s bridge relied on a 1-of-1 verifier configuration (DVN), meaning a single verifier could approve a cross-chain message. Attackers manipulated the verifier’s inputs—likely through RPC poisoning and infrastructure compromise—so the system accepted a non-existent transaction as valid. Once verified, execution via lzReceive() was permissionless, and funds were released.
The attacker then moved downstream into Aave, depositing the compromised rsETH as collateral and borrowing ETH. This converted synthetic or illegitimate value into real liquidity. As part of the response, Arbitrum froze approximately 30,000 ETH tied to the attacker through an emergency governance action.
The KelpDAO exploit wasn’t a smash-and-grab. It was a Lego tower with one invisible defect. Every block looked correct. Every connection held. But one piece—the cross-chain message—was fake. And the system believed it.

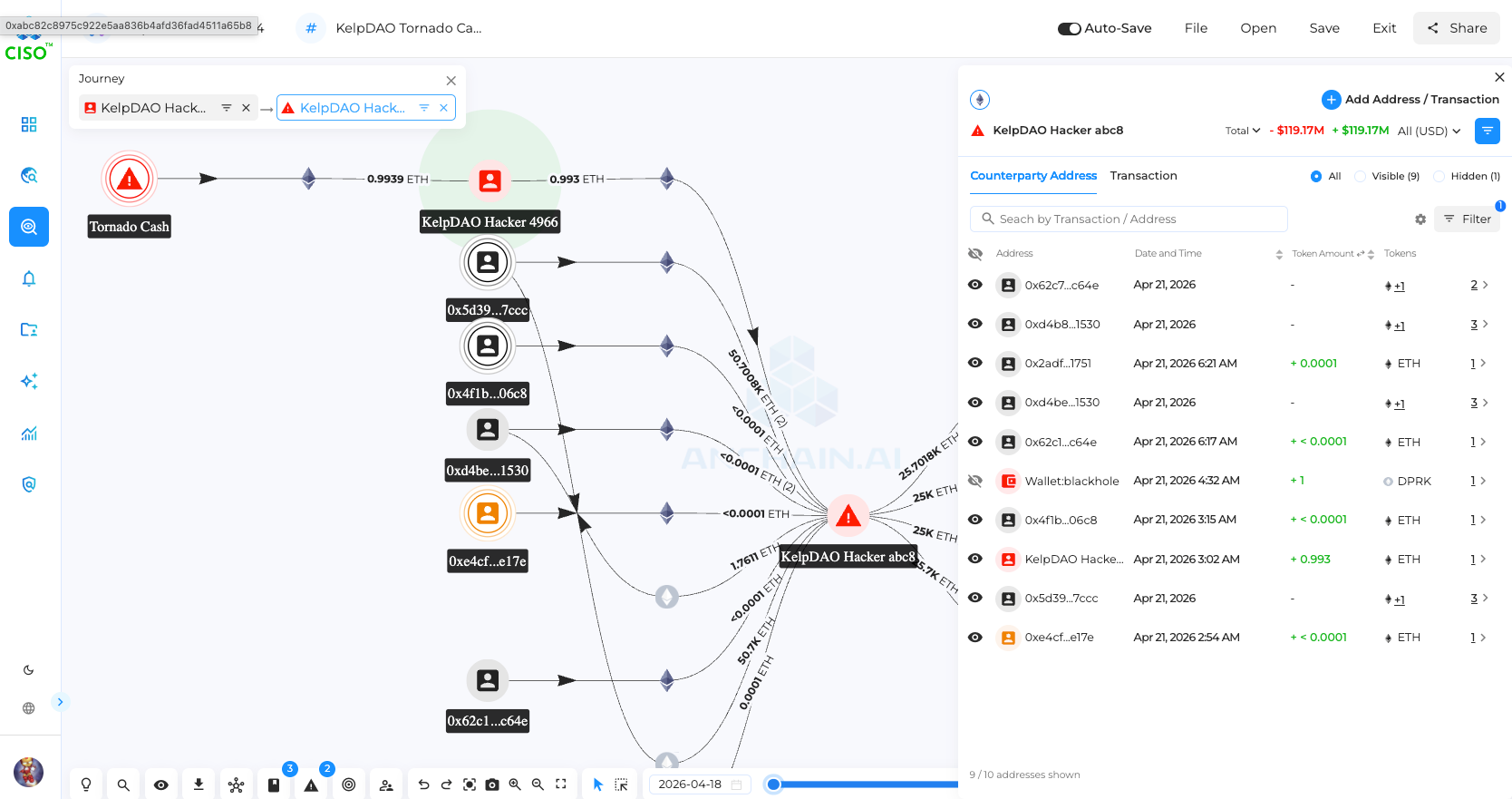
Step 0 — Pre-funding (Tornado Cash)
Figure: Attacker wallet 0x4966 funded by Tornado Cash, as shown on AnChain.ai platform: https://ciso.anchainai.com/s/5A0JvcmR88e
Step 1 — Infrastructure Compromise
Step 2 — Data Poisoning
Step 3 — Message Verification
Step 4 — Execution (Exploit Trigger)
Step 5 — DeFi Cash-out (Aave)
Step 6 — Emergency Response
Step 7 — Post-Exploit Containment
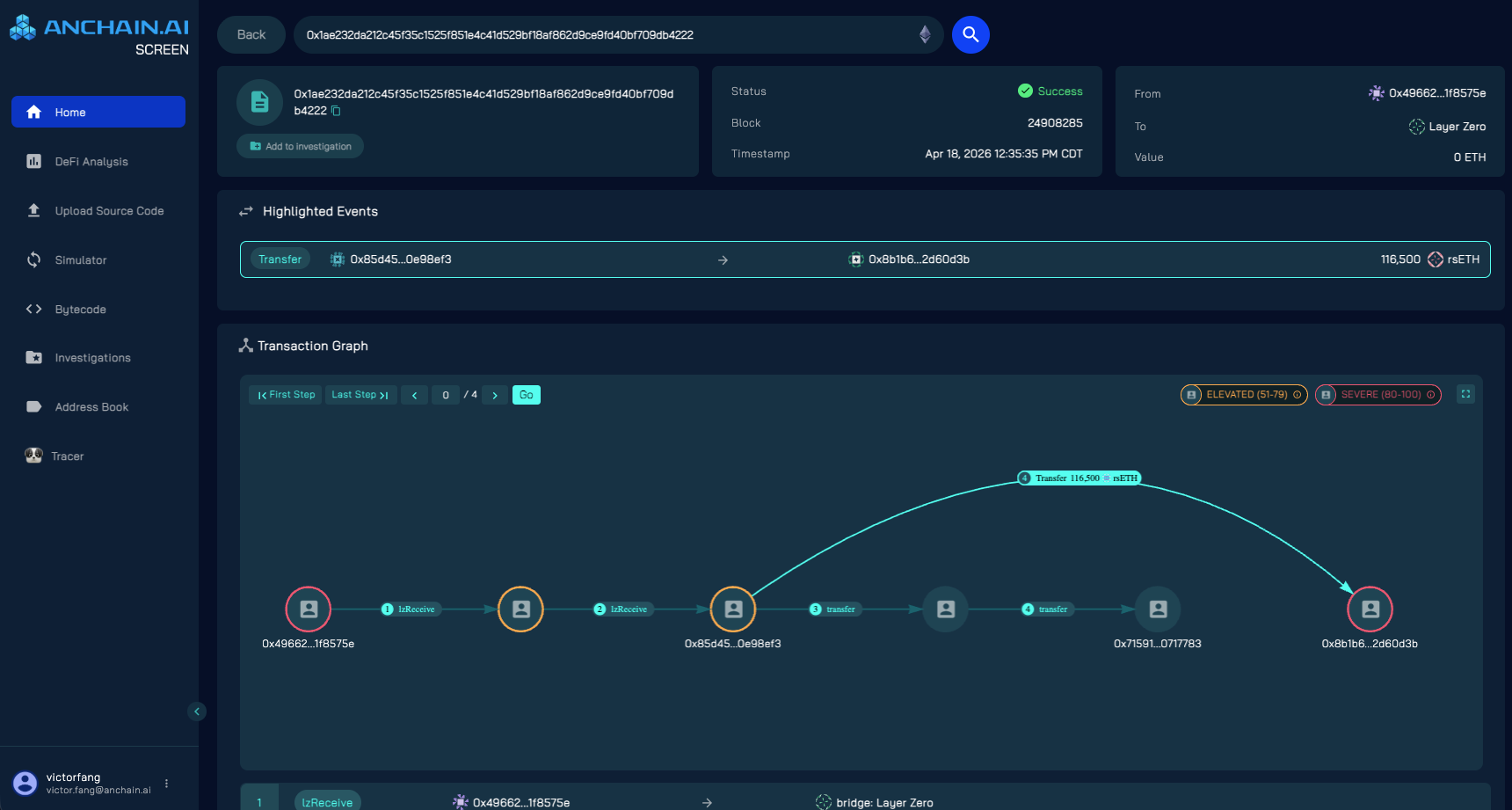
A key transaction reveals the LayerZero mechanism, which is the $290M smart contract transaction:
Tx: 0x1ae232da212c45f35c1525f851e4c41d529bf18af862d9ce9fd40bf709db4222
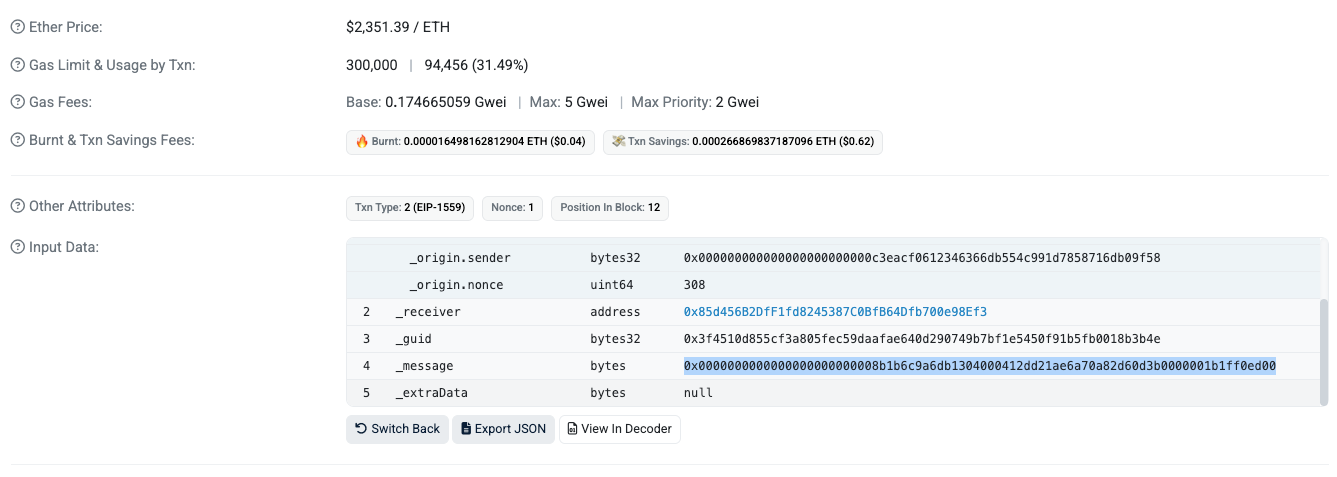
LayerZero/OFT (Omnichain Fungible Token)-style packed _message as shown on etherscan:
0x0000000000000000000000008b1b6c9a6db1304000412dd21ae6a70a82d60d3b0000001b1ff0ed00Decoded:
Interpretation: this looks like a LayerZero OFT transfer message containing a 32-byte left-padded destination address plus an 8-byte shared-decimals amount. LayerZero OFT commonly uses amountSD as uint64, then converts to local decimals on the destination chain.
Nothing about the payload is malicious. That is precisely the problem. This is where traditional auditing fails. Code can be correct, yet the DeFi can still be compromised.
Professional DeFi investigators can gain more productivity with Anchain.ai SCREEN smart contract risk platform, which can unpack the details of this malicious internal transaction, in a user friendly way.
The KelpDAO crisis closely mirrors the 2008 subprime crisis in economic structure: both systems build successive layers of financial claims on top of a base asset, then amplify returns through leverage.
DeFi flow:
ETH → stETH via Lido → rsETH via KelpDAO → collateral on Aave → leverage (looping)
Subprime flow:
Mortgages → MBS → CDO → repo financing → leverage
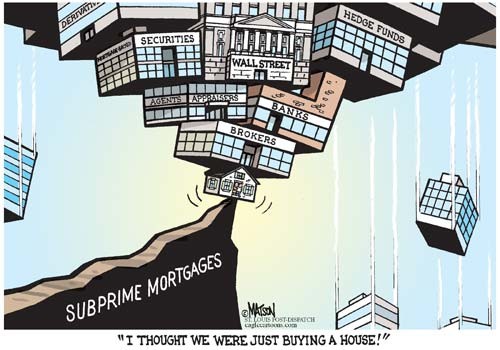
In both systems, each transformation appears rational. The goal is to increase yield and capital efficiency by stacking claims on the same underlying asset. Stability depends on one assumption: the asset—and every layer built on it—accurately reflects real value.
The failure begins when that assumption breaks.
In the subprime crisis, the weakness was at the foundation. Mortgage defaults eroded the value of MBS and CDOs, and the structure collapsed from the bottom up. In DeFi, the base asset can remain sound, but failure can emerge in the middle of the stack. In the KelpDAO case, a forged cross-chain state introduced a false layer that the system accepted as real. Everything built on top inherited that error.
The propagation is identical. Once trust in collateral is questioned, leverage unwinds, liquidity disappears, and the system destabilizes.
The key differences are speed, transparency, and response.
The underlying lesson is unchanged. When leverage is built on layered and reused collateral, the system’s stability depends entirely on the credibility of its assumptions. When those assumptions fail, the collapse is not local—it cascades
DeFi investigations can no longer rely on crypto tracing alone. Tracking fund flows shows where value moved, but not how it was created at the smart contract level. In incidents such as KelpDAO and KyberSwap, this limitation makes traditional tracing incomplete.
Smart contract forensics is now essential. Investigators must reconstruct execution paths, decode internal calls, and analyze cross-protocol interactions. The objective is not just to follow assets, but to determine whether a state transition is logically and economically valid.
At AnChain.AI, this is the problem addressed by SCREEN (https://www.anchain.ai/screen). SCREEN enables investigators to unpack complex contract behavior, decode internal transactions, and surface implausible state transitions—cases where execution is correct, but the outcome violates system reality. In the KelpDAO case, a cross-chain message via LayerZero appeared valid, yet triggered asset release without a corresponding source-chain event. That inconsistency is the signal.
As cross-chain messaging and off-chain infrastructure increasingly influence on-chain outcomes, investigators must move beyond transactions and assess the integrity of system state. DeFi forensics is evolving from tracing assets to validating reality.
DeFi works like a Lego tower—modular, composable, and powerful. The KelpDAO incident showed how it fails: not from broken blocks, but from a false connection that everything else trusted.
Fixing this requires shifting focus from code to system integrity:
This is where AnChain.AI comes in. With SCREEN Smart Contract Risk Platform (https://www.anchain.ai/screen) and expert-led investigations, AnChain enables smart contract forensics, state validation, and cross-chain risk analysis.
👉 Explore SCREEN: https://www.anchain.ai/screen
👉 Work with AnChain experts to secure your DeFi systems: https://www.anchain.ai/demo
