
On March 22, 2026, an attacker exploited Resolv Labs' USR stablecoin protocol, minting 80 million unbacked tokens from just 200,000 USDC in collateral. Within hours, they'd extracted approximately $25 million in ETH, crashed USR's price by 74%, and triggered cascading liquidations across Morpho, Fluid, and Euler. The funds were layered through intermediary wallets and routed to Binance, cross-chain bridges, and non-KYC swap services.
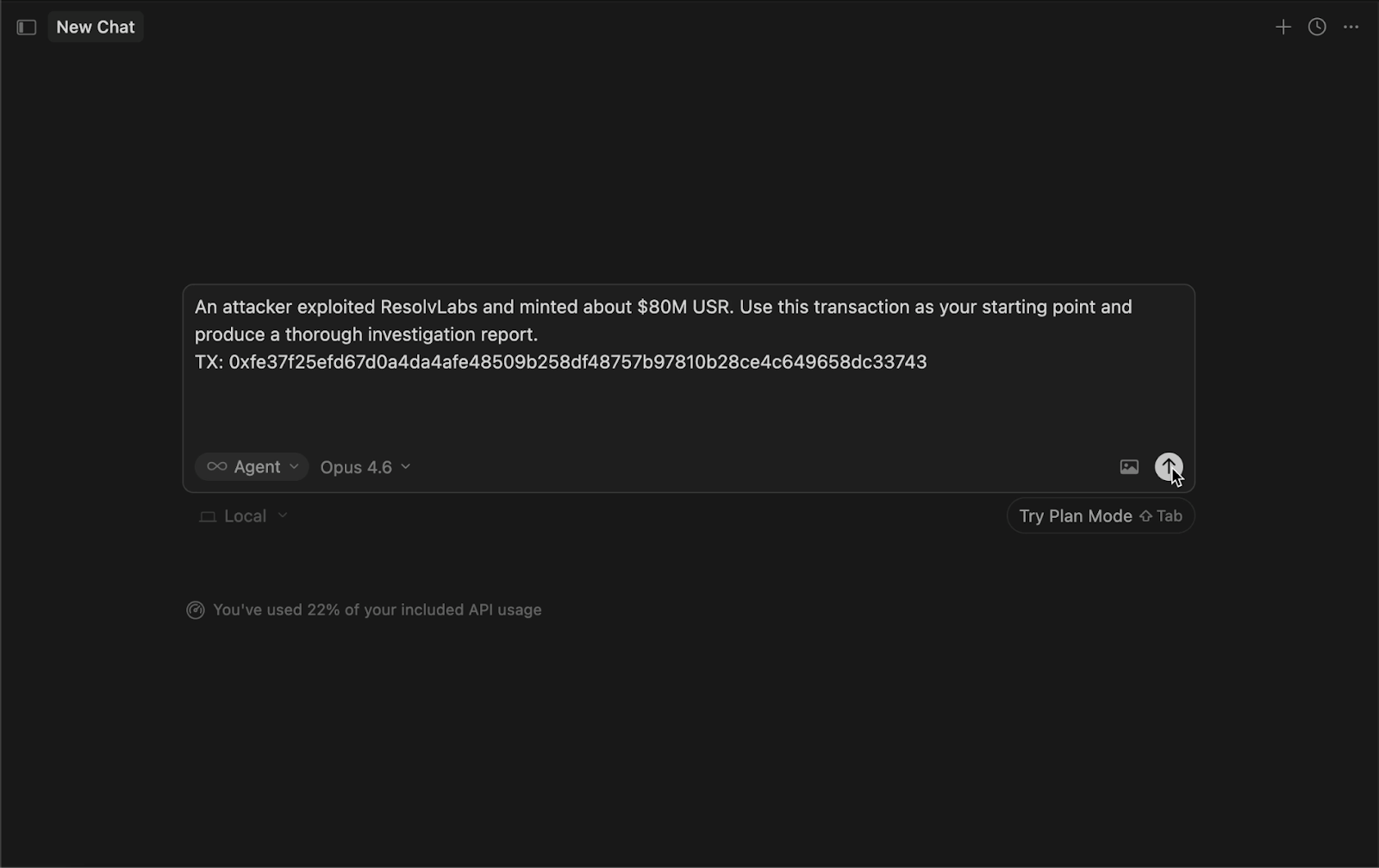
Two days later, we fed one transaction hash into an AI agent equipped with our new blockchain investigation skill. What came back was a comprehensive 13-page forensic report covering the full attack mechanism, a multi-hop fund flow analysis with entity attribution, sanctions screening on every address involved, and actionable recommendations — all anchored to on-chain evidence with block explorer links the reader can verify independently.
This is what the blockchain-investigation skill does.
Agent skill, proposed by Anthropic recently, is a structured capability that allows AI systems to execute a multi-step task with consistency and traceability. It combines:
Frameworks such as MCP Model Context Protocol and orchestration systems like LangGraph formalize how these components interact. The objective is to move beyond isolated tool calls toward repeatable workflows. In practice, a skill functions less like a feature and more like a playbook. In this case, the blockchain-investigation skill defines:
With agent skill, the LLM output becomes predictable and auditable.
A thorough blockchain investigation is slow, manual, and fragmented. The typical workflow looks something like this: pull raw transaction data from an RPC provider, decode event logs and calldata, cross-reference addresses against threat intelligence databases, screen against OFAC and global sanctions lists, trace fund flows across multiple hops and chains, compute financial impact, and synthesize everything into a report that a compliance officer or investigator can actually act on.
For a complex DeFi exploit, this process can take days. It requires fluency with multiple tools and APIs, deep protocol knowledge, and the discipline to convert raw data into something a non-developer audience can understand. The output quality depends entirely on the individual analyst — their expertise, their tooling, and how much coffee they've had. ☕️
And the demand for this work is only growing. Every DeFi exploit, every sanctions screening request, every compliance review requires the same labor-intensive cycle of data gathering, analysis, and reporting. It doesn't scale.
The blockchain-investigation skill is a collaboration between AnChain.AI and Pocket Network that gives AI agents the expertise of an experienced blockchain forensic analyst. It's not a chatbot that summarizes blockchain data — it's a structured investigation methodology that an AI agent executes autonomously, using real on-chain data and real threat intelligence tools.
The architecture is straightforward. Two complementary data layers, orchestrated by a skill that knows when to use each:
The skill sits on top of both, encoding the investigative methodology: when to triage, when to escalate, how to trace funds, how to handle off-chain intelligence, and how to write a report that a compliance team can use in a legal proceeding.
To show what this looks like in practice, we used the skill to investigate the Resolv USR exploit — a real, significant DeFi incident that happened days before our test. We gave the agent one transaction hash and a one-line description. Here's how it worked.
The agent's first move was to pull the raw transaction from Pocket Network's Ethereum RPC — the sender, the target contract, the calldata, the event logs. Within the first few tool calls, it had classified the caller as an EOA with a nonce of 26,392 (a long-lived operational key, not a fresh attack wallet), identified the target as Resolv's swap contract, and decoded the event logs to find a USDC transfer of 100,000 alongside a USR mint of approximately 50 million — a 500x amplification that immediately flagged this as abnormal.
It then ran AnChain risk scores on every address involved. All came back as 50/100 (Guarded, Unaffiliated) — which the agent correctly interpreted as a consequence of the exploit's recency rather than an indication of low risk. This kind of contextual judgment is baked into the skill's methodology.
Rather than guessing at the vulnerability, the agent worked from the evidence. It identified the function selector (`completeSwap`), decoded the parameters (a request ID, an index, and a mint amount), and observed that the mint amount bore no relationship to the deposited collateral. It then found the second minting transaction independently by tracing the SERVICE_ROLE caller's activity and confirmed the same pattern: 100,000 USDC in, 30 million USR out.
From this on-chain evidence, the agent constructed three hypotheses: compromised signing key, missing collateral validation, or oracle manipulation — and assessed their relative likelihood based on what the chain data showed. The 500x amplification with minimal capital made oracle manipulation unlikely. The high nonce on the SERVICE_ROLE account pointed toward key compromise or a validation gap.
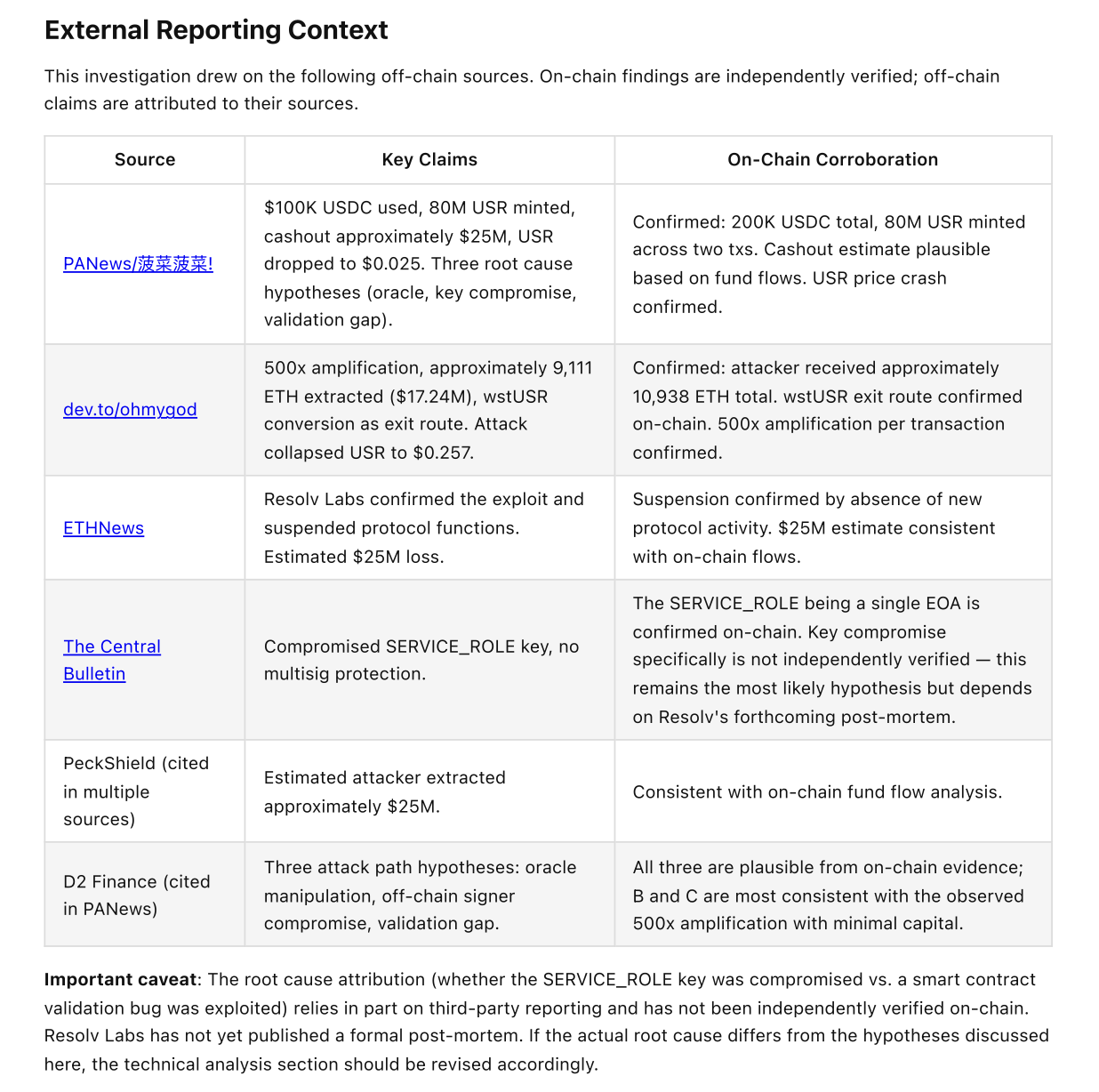
The agent also found third-party security reporting about the exploit via web search. Here's where the skill's evidence discipline matters: rather than treating these reports as established fact, the agent quarantined them in a dedicated "External Reporting Context" section, noting which claims it could corroborate on-chain and which remained unverified. The root cause attribution was explicitly flagged as dependent on external reporting that Resolv Labs had not yet confirmed.
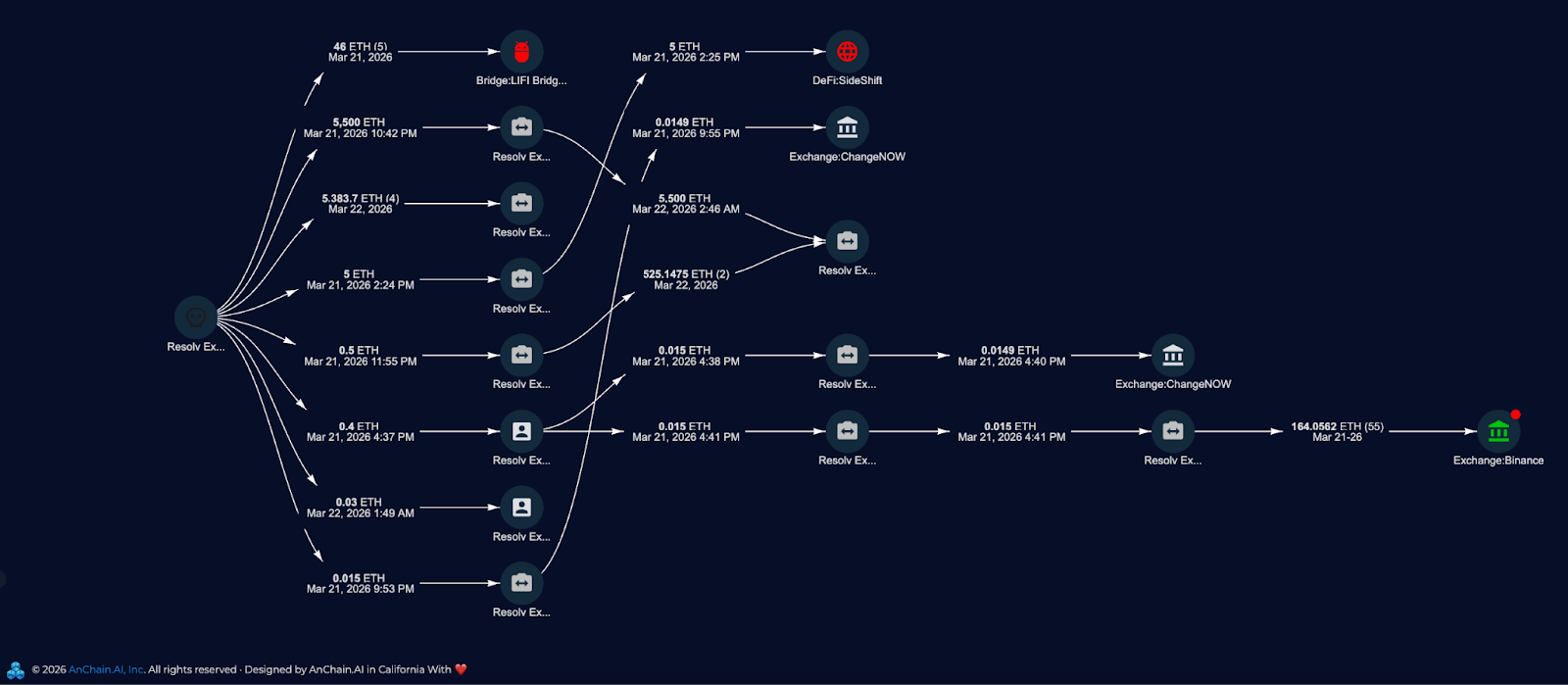
This is where AnChain's intelligence layer earns its keep. The agent ran automated fund tracing on the attacker's primary contract and mapped the full outbound flow: 80 million USR converted to wstUSR (exploiting stale derivative pricing in liquidity pools), swapped through Curve, Uniswap, and Airswap for stablecoins, converted to approximately 10,938 ETH, then layered through intermediary wallets across four hops before reaching Binance (small structured deposits), LiFi Bridge (cross-chain), SideShift, and ChangeNOW (non-KYC swap services).
The skill guided the agent to compute the actual financial impact rather than punt: approximately $25 million extracted from $200,000 in collateral, with the gap between the $80M face value of minted USR and the $25M extracted reflecting the massive slippage as the attacker dumped tokens into limited liquidity.
The final output is a comprehensive forensic report — not a data dump. The executive summary opens with what happened and why it matters, in language a compliance officer can understand. Every address and transaction hash is a clickable block explorer link. Financial figures are in human-readable denominations with USD equivalents. Technical concepts are explained for the audience, not assumed.
The report includes a threat actor profile, transaction-level attack detail, a multi-phase fund flow analysis with entity attribution, sanctions screening results, a smart contract analysis, indicators of compromise with full addresses for blocklisting, and specific recommendations for both immediate response and long-term protocol remediation.
Building an AI-powered investigation tool is easy. Building one you'd trust in a legal proceeding is hard. Here's what we focused on.
The skill builds every analysis from verified chain data before incorporating any external reporting. Off-chain intelligence — news articles, protocol post-mortems, security researcher analyses — is useful context, but it's not evidence. The skill quarantines off-chain claims, attributes them to their sources, and explicitly flags when conclusions depend on unverified reporting. The goal: a report where every factual claim can be independently verified by the reader through a block explorer link.
The people who read investigation reports — compliance officers, investigators, legal counsel, institutional investors — understand blockchain at a user level. They know what wallets, transactions, and tokens are. They don't read hex, decode ABI calldata, or think in gas units. The skill enforces presentation standards that translate raw tool output into human-readable findings: timestamps in UTC, amounts in native denomination with USD equivalents, addresses as clickable explorer links, and technical details explained in context rather than assumed.
Pocket Network's decentralized RPCs are free. AnChain's intelligence tools cost credits. The skill uses this asymmetry strategically: gather all available raw data from Pocket Network first, then spend AnChain credits only when intelligence is needed — risk scores for triage, sanctions screening for compliance, automated tracing when manual hop-by-hop analysis isn't practical. The Resolv investigation used approximately 755 AnChain credits total for a comprehensive forensic report.
Every claim in the report is anchored to something the reader can verify: a block explorer link for on-chain data, a named provider for risk scores, a specific sanctions list and entry ID for compliance findings, a source URL for off-chain intelligence. No bracket labels, no "trust me" assertions. The reader can follow the evidence trail end to end.
The blockchain-investigation skill is coming soon as a collaboration between AnChain.AI and Pocket Network. Whether you're a compliance team screening addresses, an investigator tracing stolen funds, or a protocol team responding to an incident — this skill turns hours of manual work into a single prompt.
We'll share launch details soon. In the meantime, if you're interested in early access or want to discuss how this fits into your workflow, reach out to us at
Schedule a call today : anchain.ai/demo
